In an era where cyber threats lurk around every digital corner, the stakes for businesses have never been higher. Just last year, global cybercrime costs soared past $8 trillion, with ransomware attacks alone crippling operations from small startups to Fortune 500 giants. Imagine waking up to find your customer database encrypted, your supply chain halted, or your intellectual property siphoned off by state-sponsored hackers—all because a single vulnerability went unchecked. It’s not just a nightmare; it’s the new normal.
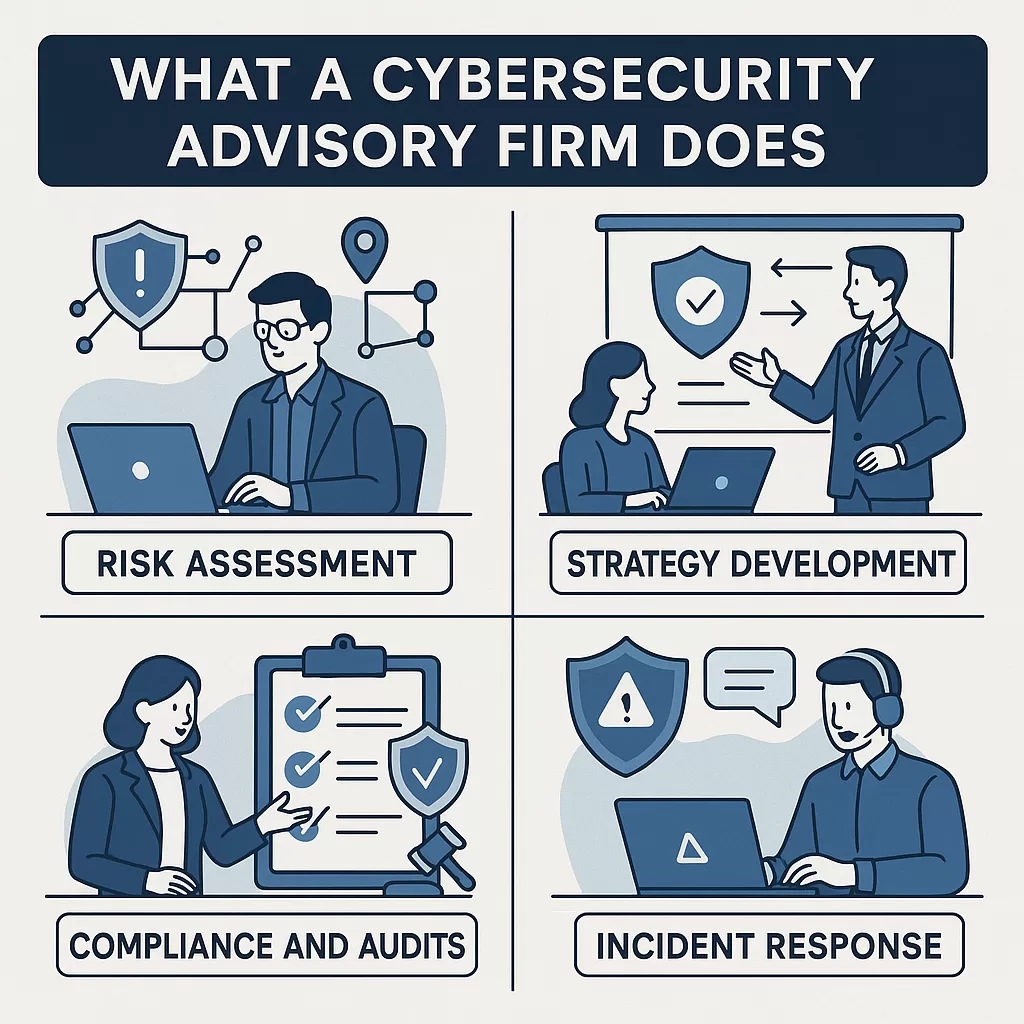
Enter the cybersecurity advisory firm: the unsung heroes of the digital battlefield. These specialized consultants don’t just sell firewalls or antivirus software; they architect entire defense ecosystems, turning reactive panic into proactive resilience. But what exactly do they do? And how does one firm, Ramabytes, stand out in this crowded field with an approach that’s as innovative as it is practical?
In this deep dive, we’ll unpack the core functions of a cybersecurity advisory firm, from risk assessments to incident response, and then zoom in on Ramabytes’ unique methodology. Drawing from years of industry evolution, we’ll explore how these firms safeguard not just data, but entire business futures. Whether you’re a C-suite executive eyeing your next security investment or an IT manager buried in alerts, this guide will demystify the advisory world and spotlight why partnering with the right firm could be your organization’s best move yet.
The Foundations: Core Functions of a Cybersecurity Advisory Firm
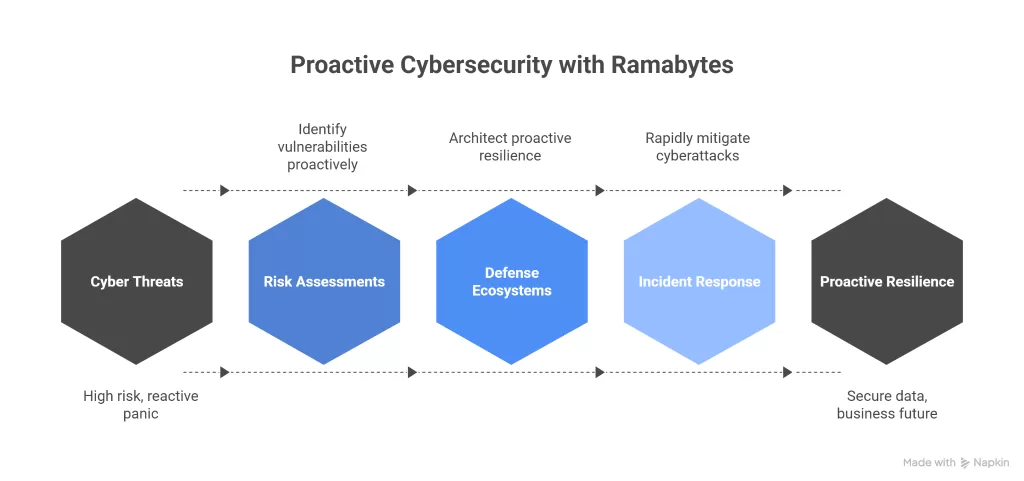
At its heart, a cybersecurity advisory firm acts as a strategic partner, bridging the gap between complex threats and actionable defenses. Unlike in-house IT teams stretched thin by daily operations, advisors bring specialized expertise to the table, offering an objective lens on vulnerabilities that internal staff might miss. Their work spans the full cybersecurity lifecycle: prevention, detection, response, and recovery. Let’s break it down.
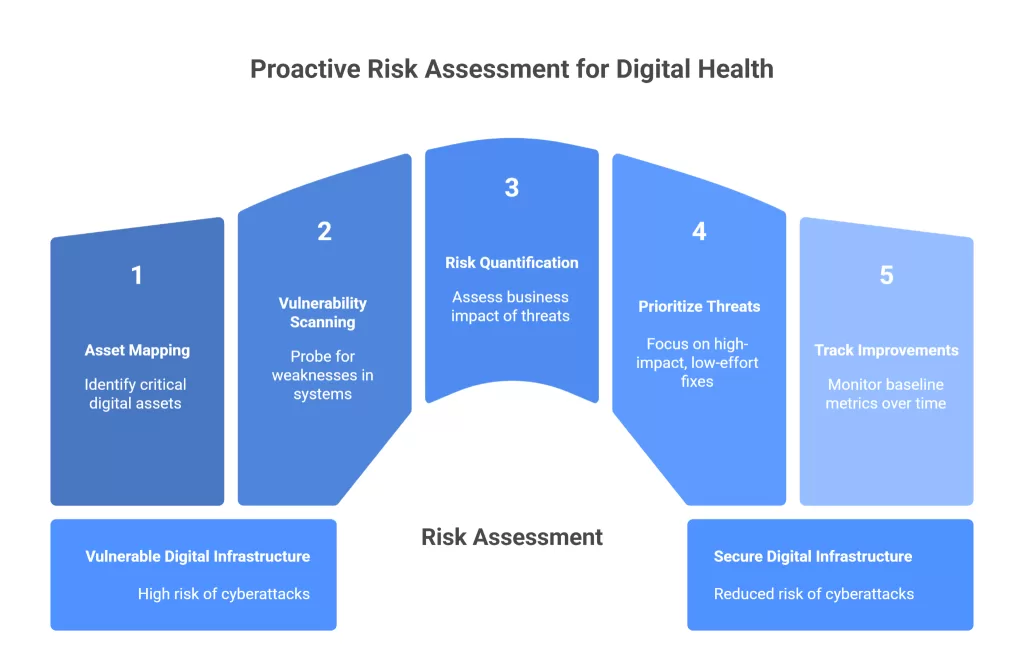
Risk Assessment: The Diagnostic Pulse Check
Every advisory engagement starts with a thorough risk assessment—think of it as a full-body scan for your digital health. Advisors dive deep into your infrastructure, mapping out assets like servers, cloud environments, endpoints, and third-party integrations. They identify vulnerabilities using tools like penetration testing (ethical hacking to simulate attacks) and vulnerability scanning software that probes for weaknesses in code, configurations, or unpatched systems.
For instance, a typical assessment might reveal that 70% of breaches stem from outdated software or misconfigured access controls. Advisors quantify these risks—not just in technical terms, but in business impact. What’s the potential financial hit from a data leak? How about reputational damage or regulatory fines under GDPR or HIPAA? By assigning risk scores (often via frameworks like NIST or ISO 27001), they prioritize threats: high-impact, low-effort fixes first.
This phase isn’t a one-off; it’s iterative. Advisors recommend baseline metrics, like mean time to detect (MTTD) threats, and track improvements over time. In essence, they’re your early warning system, ensuring you’re not blindsided by the next SolarWinds-style supply chain attack.
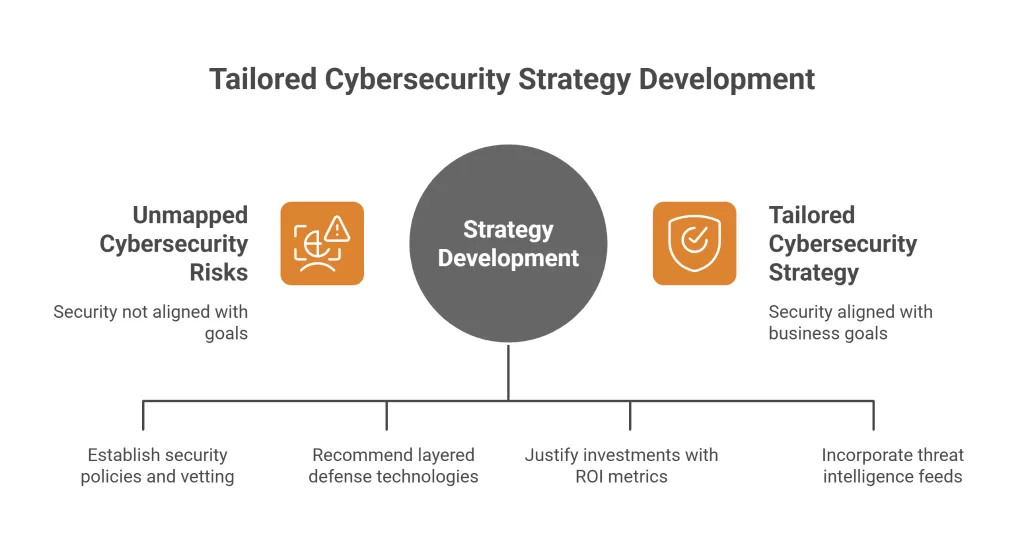
Strategy Development: Building the Fortress Blueprint
Once risks are mapped, advisors craft a tailored cybersecurity strategy—a roadmap that aligns security with business goals. This isn’t boilerplate advice; it’s customized to your industry, size, and risk appetite. For a fintech firm, that might mean zero-trust architecture, where no user or device is inherently trusted. For a healthcare provider, it could involve HIPAA-compliant data segmentation.
Key elements include:
- Governance Frameworks: Establishing policies for everything from password hygiene to vendor vetting.
- Technology Roadmaps: Recommending layered defenses like next-gen firewalls, AI-driven anomaly detection, and secure access service edge (SASE) for remote workforces.
- Budget Optimization: Advisors help justify investments, showing ROI through metrics like reduced breach probability (often 40-60% post-implementation).
Strategy isn’t static; it’s adaptive. With AI-powered threats evolving daily—think deepfake phishing or polymorphic malware—advisors incorporate threat intelligence feeds, forecasting trends like quantum-resistant encryption for future-proofing.
Compliance and Audits: Navigating the Regulatory Maze
Compliance isn’t sexy, but it’s non-negotiable. Advisors excel at demystifying regulations, from PCI-DSS for payments to SOC 2 for cloud services. They conduct gap analyses, pinpointing where your controls fall short, and guide remediation—whether that’s automating audit trails or training staff on data privacy.
Audits go beyond checklists. External-facing ones build trust with partners; internal ones foster a security-first culture. Advisors often simulate regulatory scrutiny, preparing you for inevitable inquiries. In a post-Equifax world, where fines can exceed $100 million, this service alone can save fortunes.
Incident Response Planning: Preparing for the Inevitable
No strategy is foolproof, so advisors design incident response (IR) plans—playbooks for when things go south. This includes tabletop exercises where teams role-play a ransomware hit, honing coordination between IT, legal, and PR.
Core components:
- Detection and Containment: Integrating SIEM (Security Information and Event Management) tools for real-time alerts.
- Forensics and Recovery: Outlining data backups, isolation protocols, and post-mortem reviews to learn from breaches.
- Crisis Communication: Templates for notifying stakeholders, minimizing panic and legal exposure.
Advisors often provide 24/7 retainer services, acting as virtual CISOs during crises. Their value? Speed. Firms with drilled IR plans recover 50% faster, per industry benchmarks.
Training and Awareness: The Human Firewall
Technology fails if people falter. Advisors deliver phishing simulations, role-based training, and awareness campaigns that make security intuitive. For executives, it’s executive briefings on board-level risks; for devs, secure coding workshops. Metrics track engagement—click rates on fake phishing emails drop dramatically post-training.
In sum, these functions form a holistic shield. Advisory firms don’t just patch holes; they engineer resilience, turning cybersecurity from a cost center into a competitive edge. But theory only goes so far—let’s see how Ramabytes brings this to life.
Ramabytes: A Holistic IT Powerhouse with Cybersecurity at Its Core
Founded in Delhi, India, Ramabytes isn’t your typical cybersecurity silo. As a full-spectrum IT consultancy, they’ve spent years honing expertise across software development, mobile apps, digital marketing, and enterprise solutions. Led by—a visionary with a track record in scaling tech ecosystems—alongside Chief Business Officer Swadesh Bansal and CFO Anil Aggarwal, the firm embodies agile innovation. Their mission? To empower businesses with cutting-edge tech that doesn’t just perform but protects.
Cybersecurity isn’t an add-on for Ramabytes; it’s woven into their DNA. Recognizing that 95% of breaches involve human error or outdated systems, they position advisory services as the linchpin of digital transformation. In a portfolio dominated by custom software and cloud migrations, their cyber arm ensures every project launches fortified. Clients span e-commerce startups to global enterprises, all benefiting from Ramabytes’ global reach and India-rooted cost efficiencies.
What sets Ramabytes apart? Their “Proactive Resilience Framework”—a proprietary blend of assessment, implementation, and continuous optimization. Unlike firms peddling off-the-shelf audits, Ramabytes treats cybersecurity as an ecosystem, integrating it seamlessly with your IT stack. Their certified experts—holding creds like CISSP, CISM, and CEH—don’t just advise; they co-build solutions, ensuring buy-in from day one.
Ramabytes’ Proactive Approach: From Assessment to Adaptation
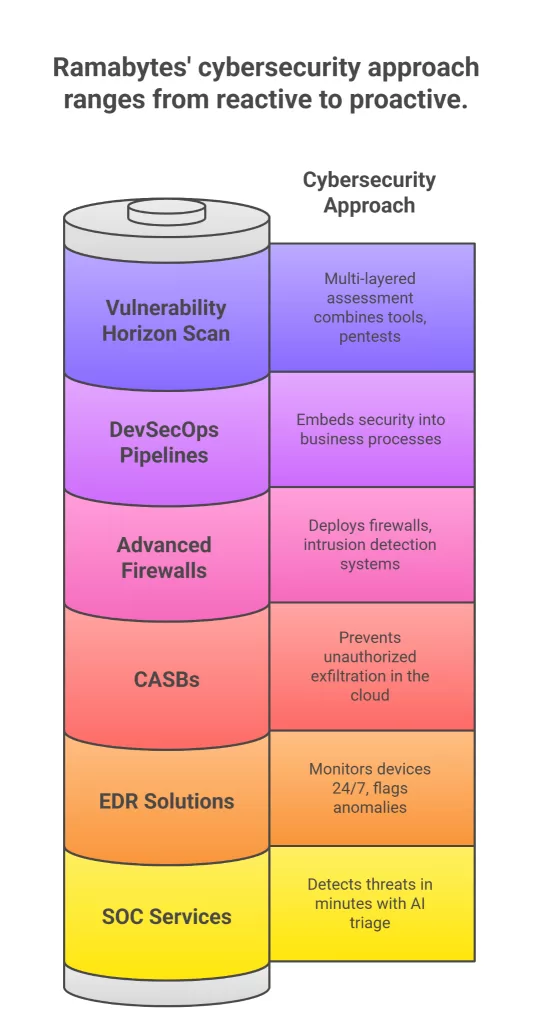
At the core of Ramabytes’ methodology is proactivity. They start with a “Vulnerability Horizon Scan,” a multi-layered assessment that combines automated tools with manual pentests. This isn’t surface-level; it drills into network topologies, endpoint inventories, and even shadow IT—those rogue apps employees love. Using frameworks like MITRE ATT&CK, they map threats to your specifics, delivering a risk heat map with prioritized actions.
Take network security: Ramabytes deploys advanced firewalls and intrusion detection systems (IDS) as your perimeter guard. But they go further, implementing Network Access Control (NAC) policies that enforce zero-trust principles. Only verified devices and users gain entry, with seamless integration into your existing ecosystem—be it Azure, AWS, or on-prem setups. In one engagement, they helped a mid-sized retailer segment their network, slashing lateral movement risks by 75% during simulated attacks.
Data protection is another pillar. Ramabytes excels in encryption—both at rest (via AES-256 standards) and in transit (TLS 1.3)—ensuring compliance with GDPR, CCPA, and beyond. Their data classification service categorizes assets by sensitivity: public, internal, confidential, restricted. Policies follow, dictating handling from labeling to secure sharing. For a healthcare client migrating to the cloud, Ramabytes implemented Cloud Access Security Brokers (CASBs), preventing unauthorized exfiltration while enabling seamless workflows.
Endpoint security? Real-time. Their endpoint detection and response (EDR) solutions monitor devices 24/7, using behavioral analytics to flag anomalies like unusual file access. Paired with Data Loss Prevention (DLP) tools, they block leaks—scanning emails, USBs, and uploads for sensitive patterns. Ramabytes’ DLP isn’t punitive; it’s educational, alerting users to near-misses and feeding into personalized training modules.
Monitoring via Security Operations Centers (SOCs) rounds out the defense. Ramabytes offers managed SOC services, blending AI triage with human oversight. Threats are detected in minutes, not hours, with automated playbooks for containment. Their SOC integrates threat intelligence from global feeds, adapting to trends like AI-generated malware.
But Ramabytes’ approach shines in governance and strategy. They develop bespoke frameworks that embed security into business processes—think DevSecOps pipelines where code scans happen pre-commit. Compliance audits are proactive, with dashboards tracking metrics against benchmarks. And for IR? Their plans include war-gaming sessions, ensuring teams respond like clockwork.
Unique to Ramabytes is their “Integrated Resilience Score”—a quarterly KPI dashboard that quantifies your posture across pillars: prevention (e.g., patch coverage), detection (MTTD), response (MTTR), and recovery (RTO). It’s gamified for stakeholders, turning dry reports into actionable insights.
Tailored Services: Customization Meets Expertise
Ramabytes’ team of 50+ certified pros brings depth across domains. NAC specialists ensure granular access—role-based, contextual, adaptive. Data experts craft DLP policies that evolve with your data flows, using machine learning to refine rules. Their training? Immersive, with VR simulations for phishing drills, boosting retention by 40%.
For enterprises, Ramabytes scales with hybrid models: advisory retainers for strategy, project-based for implementations, managed services for ops. Small businesses get “Cyber Starter Packs”—affordable assessments plus quick wins like MFA rollouts. Across the board, they emphasize ROI: one client recouped advisory fees in months via avoided fines.
Hypothetically, picture a SaaS provider partnering with Ramabytes post-breach. The scan uncovers API flaws; strategy implements API gateways with rate limiting. SOC monitoring catches a DDoS attempt early, while training curbs insider risks. Result? Uptime jumps 99.9%, customer trust rebounds.
The Tangible Impact: Why Ramabytes’ Approach Delivers Results
Partnering with a firm like Ramabytes yields measurable wins. Breaches cost $4.45 million on average; their proactive stance can halve that through early detection. Compliance becomes a byproduct, not a burden—fewer audits, smoother certifications. Culturally, security shifts from “IT’s problem” to “our advantage,” fostering innovation without fear.
In a threat landscape where quantum computing looms and AI adversaries multiply, Ramabytes’ blend of human ingenuity and tech prowess positions clients ahead. Their Delhi base means agile, cost-effective delivery without sacrificing quality—global expertise at local speeds.
Conclusion: Secure Your Tomorrow Today
Cybersecurity advisory firms like Ramabytes aren’t luxuries; they’re necessities in our hyper-connected world. They do more than assess risks—they architect futures where threats are anticipated, not endured. By explaining Ramabytes’ proactive, integrated approach, we’ve seen how tailored guidance turns vulnerabilities into strengths.
If your organization feels the cyber pinch, it’s time to act. Engage an advisor not for audits alone, but for partnership. With Ramabytes leading the charge, your digital fortress isn’t just built—it’s unbreakable. What’s your first step? A risk scan? Strategy session? The resilient path starts now.